Who Was the NSA Contractor Arrested for Leaking the ‘Shadow Brokers’ Hacking Tools?
In August 2016, a mysterious entity calling itself “The Shadow Brokers” began releasing the first of several troves of classified documents and hacking tools purportedly stolen from “The Equation Group,” a highly advanced threat actor that is suspected of having ties to the U.S. National Security Agency. According to media reports, at least some of the information was stolen from the computer of an unidentified software developer and NSA contractor who was arrested in 2015 after taking the hacking tools home. In this post, we’ll examine clues left behind in the leaked Equation Group documents that may point to the identity of the mysterious software developer.

The headquarters of the National Security Agency in Fort Meade, Md.
The existence of the Equation Group was first posited in Feb. 2015 by researchers at Russian security firm Kaspersky Lab, which described it as one of the most sophisticated cyber attack teams in the world.
According to Kaspersky, the Equation Group has more than 60 members and has been operating since at least 2001. Most of the Equation Group’s targets have been in Iran, Russia, Pakistan, Afghanistan, India, Syria, and Mali.
Although Kaspersky was the first to report on the existence of the Equation Group, it also has been implicated in the group’s compromise. Earlier this year, both The New York Times and The Wall Street Journal cited unnamed U.S. intelligence officials saying Russian hackers were able to obtain the advanced Equation Group hacking tools after identifying the files through a contractor’s use of Kaspersky Antivirus on his personal computer. For its part, Kaspersky has denied any involvement in the theft.
The Times reports that the NSA has active investigations into at least three former employees or contractors, including two who had worked for a specialized hacking division of NSA known as Tailored Access Operations, or TAO.
Thanks to documents leaked from former NSA contractor Edward Snowden we know that TAO is a cyber-warfare intelligence-gathering unit of NSA that has been active since at least 1998. According to those documents, TAO’s job is to identify, monitor, infiltrate and gather intelligence on computer systems being used by entities foreign to the United States.
The third person under investigation, The Times writes, is “a still publicly unidentified software developer secretly arrested after taking hacking tools home in 2015, only to have Russian hackers lift them from his home computer.”
JEEPFLEA & EASTNETS
So who are those two unnamed NSA employees and the contractor referenced in The Times’ reporting? The hacking tools leaked by The Shadow Brokers are now in the public domain and can be accessed through this Github repository. The toolset includes reams of documentation explaining how the cyber weapons work, as well as details about their use in highly classified intelligence operations abroad.
Several of those documents are Microsoft Powerpoint (.pptx) and PDF files. These files contain interesting metadata that includes the names of at least two people who appear to be connected to the NSA’s TAO operations.
Inside the unzipped folder there are three directories: “oddjob,” “swift,” and “windows.” Looking at the “swift” folder, we can see a Powerpoint file called “JFM_Status.pptx.”
JFM stands for Operation Jeepflea Market, which appears to have been a clandestine operation aimed at siphoning confidential financial data from EastNets — a middle eastern partner in SWIFT. Short for the Society for Worldwide Interbank Financial Telecommunication, SWIFT provides a network that enables financial institutions worldwide to send and receive data about financial transactions.
Each of the Jeepflea Powerpoint slides contain two overlapping seals; one for the NSA and another for an organization called the Central Security Service (CSS). According to Wikipedia, the CSS was formed in 1972 to integrate the NSA and the Service Cryptologic Elements (SCE) of the U.S. armed forces.
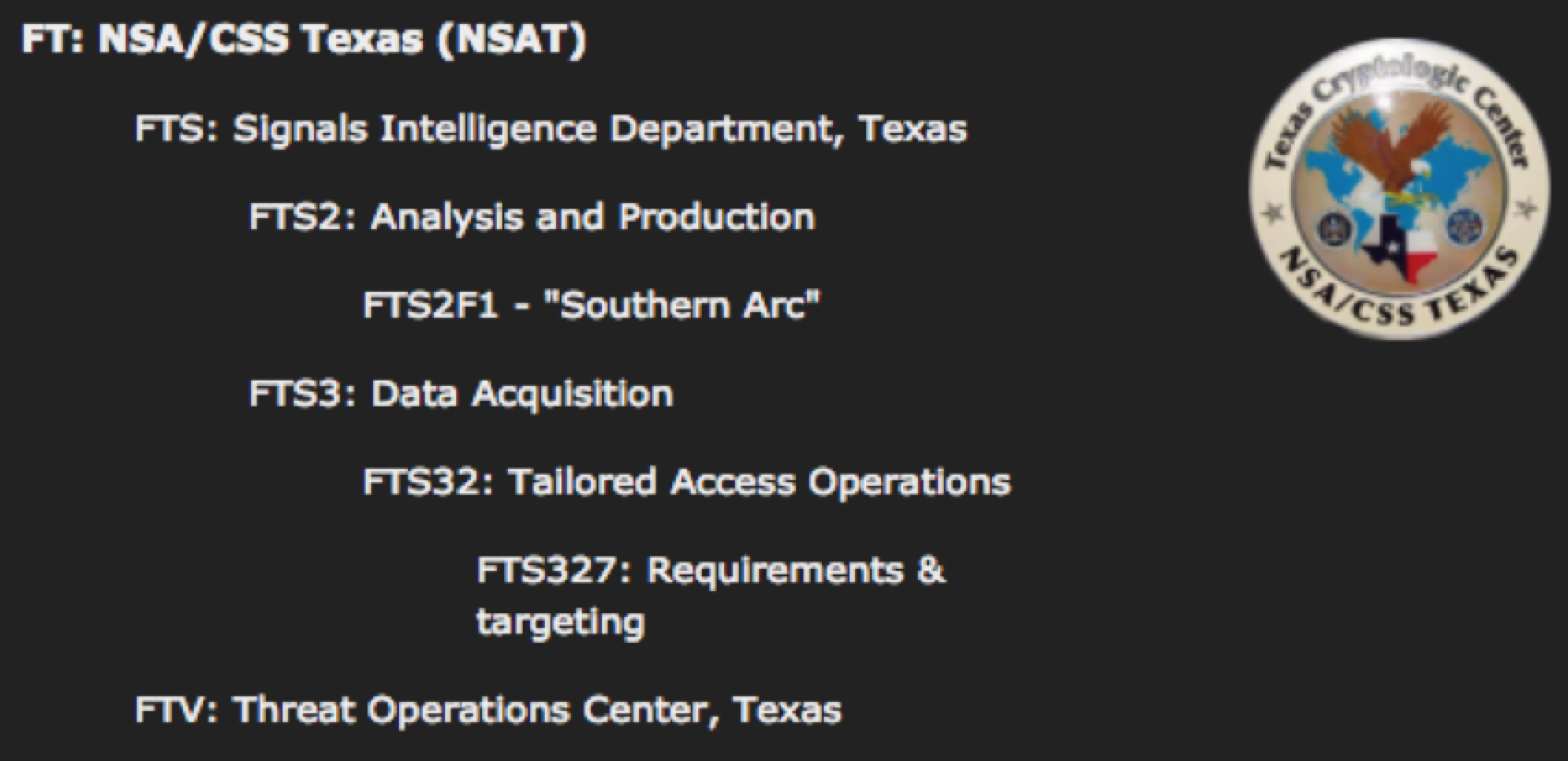
In Figure 10 of the Jeepflea Powerpoint document, we can see the seal of the Texas Cryptologic Center, a NSA/CSS entity that is based out of Lackland Air Force Base in San Antonio Texas.
The metadata contained in the Powerpoint document shows that the last person to modify it has the designation “NSA-FTS32 USA,” and that this leaked version is the 9th revision of the document. What does NSA-FTS32 mean? According to multiple sources on the internet it means Tailored Access Operations.
We can also see that the creator of the Jeepflea document is the same person who last modified it. The metadata says it was last modified on 8/12/2013 at 6:52:27 PM and created on 7/1/2013 at 6:44:46 PM.
The file JFMStatus.pptx contains metadata showing that the creator of the file is one Michael A. Pecoraro. Public record searches suggest Mr. Pecoraro is in his mid- to late 30s and is from San Antonio, Texas. Pecoraro’s name appears on multiple documents in The Shadow Brokers collection. Mr. Pecoraro could not be reached for comment.
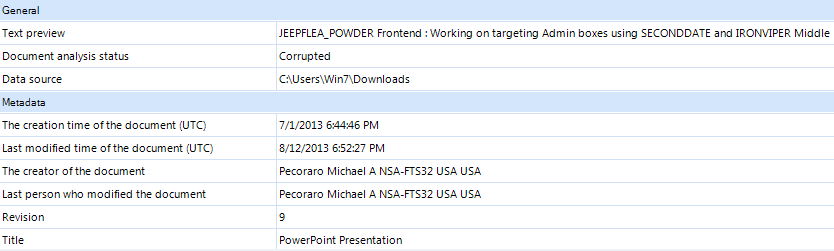
The metadata in a Microsoft Powerpoint presentation on Operation Jeepflea shows that the document was created and last modified in 2013 by a Michael A. Pecoraro.
Another person who earned the NSA-FTS32 designation in the document metadata was Nathan S. Heidbreder. Public record searches suggest that Mr. Heidbreder is approximately 30 years old and has lived in San Antonio and at Goodfellow Air Force Base in Texas, among other locations in the state.
According to Goodfellow’s Wikipedia entry, the base’s main mission is cryptologic and intelligence training for the Air Force, Army, Coast Guard, Navy, and Marine Corps. Mr. Heidbreder likewise could not be reached for comment.
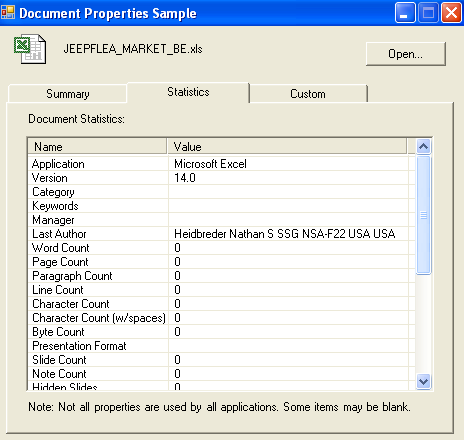
The metadata contained in one of the classified Jeepflea Market Microsoft Excel documents released in The Shadow Brokers trove states that a Nathan S. Heidbreder was the last person to edit the document.
Another file in the leaked Shadow Brokers trove related to this Jeepflea/EastNets operation is potentially far more revealing, mainly because it appears to have last been touched not by an NSA employee, but by an outside contractor.
That file, “Eastnets_UAE_BE_DEC2010.vsd,” is a Microsoft Visio document created in Sept. 2013. The metadata inside of it says the last user to open the file was one Gennadiy Sidelnikov. Open records searches return several results for this name, including a young business analyst living in Moscow and a software developer based in Maryland.
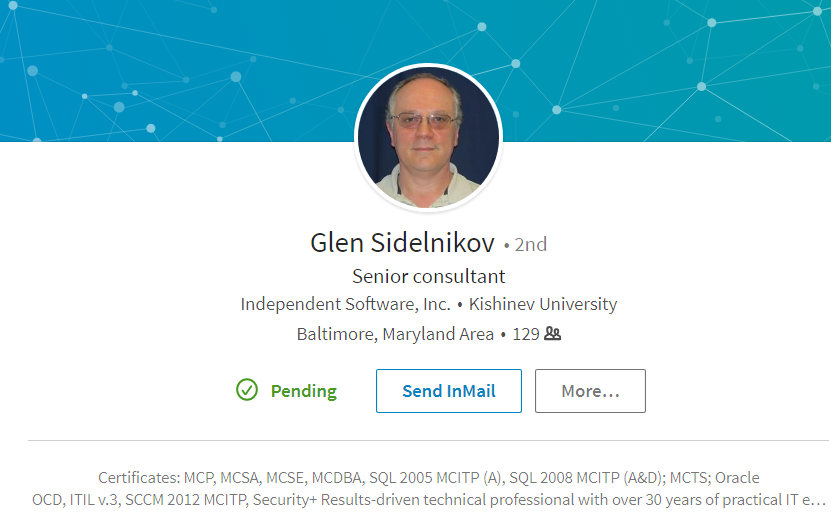
As the NSA is based in Fort Meade, Md., this latter option seems far more likely. A brief Internet search turns up a 50-something database programmer named Gennadiy “Glen” Sidelnikov who works or worked for a company called Independent Software in Columbia, Md. (Columbia is just a few miles away from Ft. Meade).
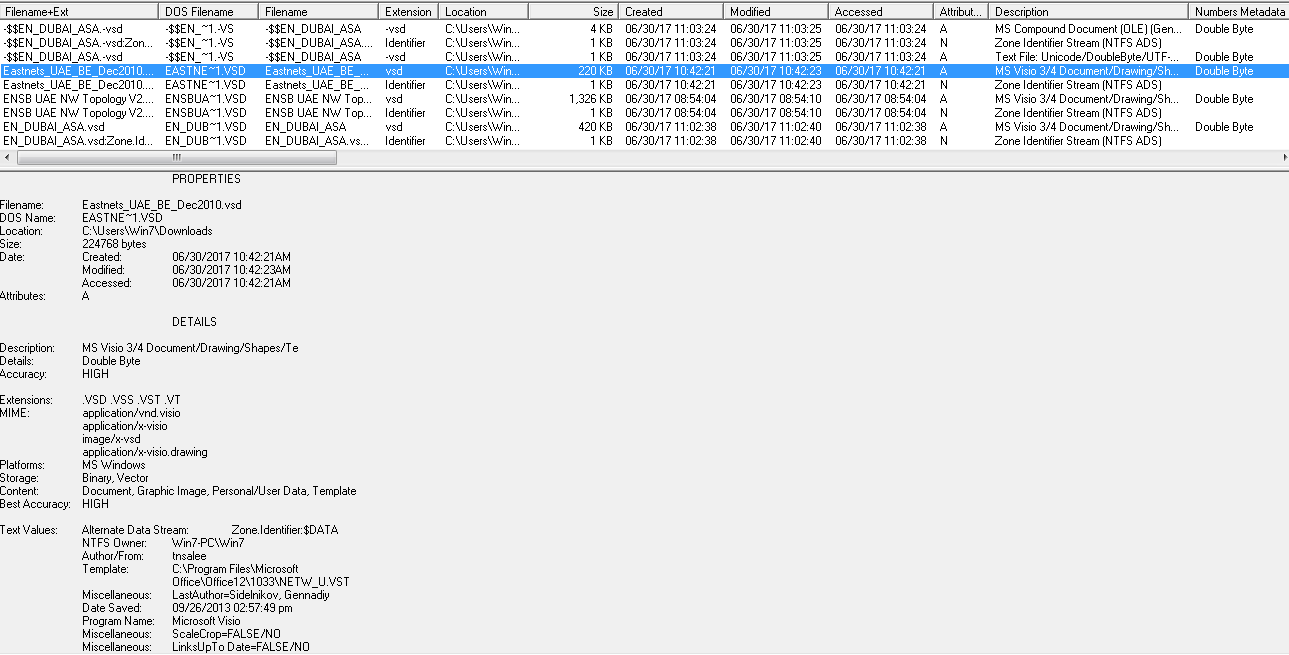
The metadata contained within Eastnets_UAE_BE_Dec2010.vsd says Gennadiy Sidelnikov is the last author of the document. Click to enlarge.
What is Independent Software? Their Web site states that Independent Software is “a professional services company providing Information Technology products and services to mission-oriented Federal Civilian Agencies and the DoD. The company has focused on support to the Intelligence Community (IC) in Maryland, Florida, and North Carolina, as well as select commercial client markets outside of the IC.”
Indeed, this job advertisement from August 2017 for a junior software engineer at Independent Software says a qualified applicant will need a TOP SECRET clearance and should be able to pass a polygraph test.
WHO IS GLEN SIDELNIKOV?
The two NSA employees are something of a known commodity, but the third individual — Mr. Sidelnikov — is more mysterious. Sidelnikov did not respond to repeated requests for comment. Independent Software also did not return calls and emails seeking comment.
Sidelnikov’s LinkedIn page (PDF) says he began working for Independent Software in 2015, and that he speaks both English and Russian. In 1982, Sidelnikov earned his masters in information security from Kishinev University, a school located in Moldova — an Eastern European country that at the time was part of the Soviet Union.
Sildelnikov says he also earned a Bachelor of Science degree in “mathematical cybernetics” from the same university in 1981. Under “interests,” Mr. Sidelnikov lists on his LinkedIn profile Independent Software, Microsoft, and The National Security Agency.
Both The Times and The Journal have reported that the contractor suspected of leaking the classified documents was running Kaspersky Antivirus on his computer. It stands to reason that as a Russian native, Mr. Sildelnikov might be predisposed to using a Russian antivirus product.
Mr. Sidelnikov calls himself a senior consultant, but the many skills he self-described on his LinkedIn profile suggest that perhaps a better title for him would be “database administrator” or “database architect.”
A Google search for his name turns up numerous forums dedicated to discussions about administering databases. On the Web forum sqlservercentral.com, for example, a user named Glen Sidelnikov is listed as a “hall of fame” member for providing thousands of answers to questions that other users posted on the forum.
KrebsOnSecurity was first made aware of the metadata in the Shadow Brokers leak by Mike Poor, Rob Curtinseufert, and Larry Pesce. All three are security experts with InGuardians, a Washington, D.C.-based penetration testing firm that gets paid to break into companies and test their cybersecurity defenses.
Poor, who serves as president and managing partner of InGuardians, said he and his co-workers initially almost overlooked Sidelnikov’s name in the metadata. But he said the more they looked into Sidelnikov the less sense it made that his name was included in the Shadow Brokers metadata at all.
“He’s a database programmer, and they typically don’t have access to operational data like this,” Poor said. “Even if he did have access to an operational production database, it would be highly suspect if he accessed classified operation documents.”
Poor said that as the data owner, the NSA likely would be reviewing file access of all classified documents and systems, and it would definitely have come up as a big red flag if a software developer accessed and opened classified files during some routine maintenance or other occasion.
“He’s the only one in there that is not Agency/TAO, and I think that poses important questions,” Poor said. “Such as why did a DB programmer for a software company have access to operational classified documents? If he is or isn’t a source or a tie to Shadow Brokers, it at least begets the question of why he accessed classified operational documents.”
Curtinseufert said it may be that Sidelnikov’s skills came in handy in the Jeepflea operations, which appear to have involved compromising large financial databases, and querying those for very specific transactions.
For example, Jeepflea apparently involved surreptitiously injecting database queries into the SWIFT Alliance servers, which are responsible for handling the messaging tied to SWIFT financial transactions.
“It looks like the SWIFT data the NSA was collecting relied heavily on databases, and they were apparently also using some exploits to gather data,” Curtinseufert said. “The SWIFT databases are all records of financial transactions, and in Jeepflea they were able to query those SWIFT databases and see who’s moving money where. They were looking to pull SWIFT data on who was moving money around the Middle East. They did this with EastNets, and they tried to do it down in Venezuela. And it looks like through EastNets they were able to hack individual banks.”
The NSA did not respond to requests for comment.
InGuardians president Poor said we may never know for sure who was responsible for the Shadow Brokers leak, an incident that has been called “one of the worst security debacles ever to befall American intelligence.” But one thing seems certain.
“I think it’s time that we state what we all know,” Poor said. “The Equation Group is Tailored Access Operations. It is the NSA.”
Tags: Central Security Service, Edward Snowden, Gennadiy Sidelnikov, Glen Sidelnikov, Goodfellow Air Force Base, Independent Software, InGuardians, Kaspersky Antivirus, Kaspersky Lab, Kishinev University, Lackland Air Force Base, Michael A. Pecoraro, Mike Poor, Nathan S. Heidbreder, national security agency, NSA hack, NSA-FTS32 USA, Operation Jeepflea Market, Rob Curtinseufert, Service Cryptologic Elements, Society for Worldwide Interbank Financial Telecommunication, SWIFT, tailored access operations, TAO, Texas Cryptologic Center, The Shadow Brokers
You can skip to the end and leave a comment. Pinging is currently not allowed.
