Instagram’s New Security Tools are a Welcome Step, But Not Enough
Instagram users should soon have more secure options for protecting their accounts against Internet bad guys. On Tuesday, the Facebook-owned social network said it is in the process of rolling out support for third-party authentication apps. Unfortunately, this welcome new security offering does nothing to block Instagram account takeovers when thieves manage to hijack a target’s mobile phone number — an increasingly common crime.
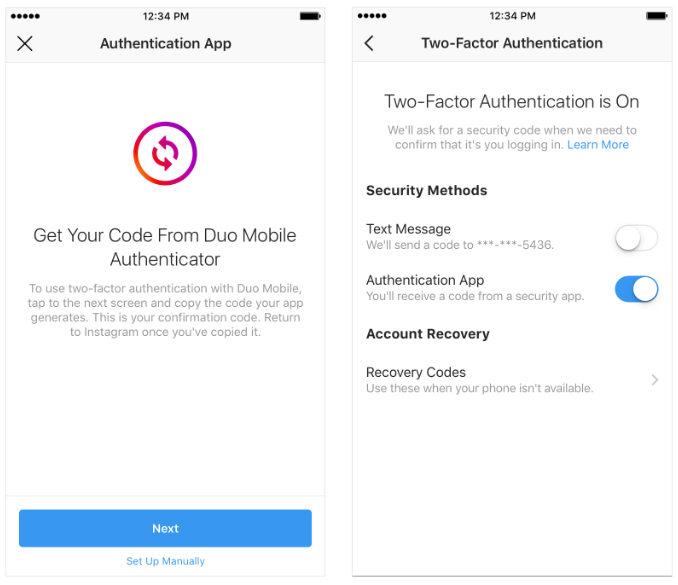
New two-factor authentication options Instagram says it is rolling out to users over the next few weeks.
For years, security experts have warned that hackers are exploiting weak authentication at Instagram to commandeer accounts. Instagram has long offered users a security option to have a one-time code sent via text message to a mobile device, but these codes can be intercepted via several methods (more on that in a bit).
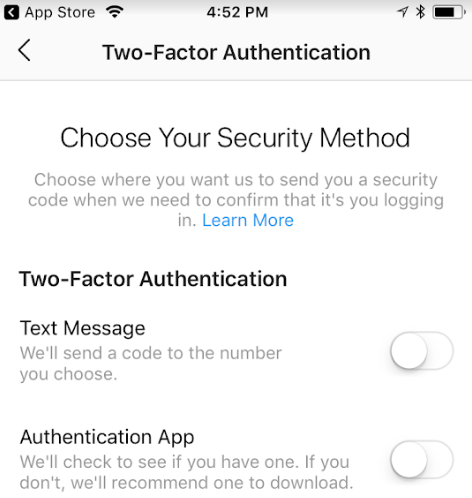
The new authentication offering requires users to download a third-party app like Authy, Duo or Google Authenticator, which generates a one-time code that needs to be entered after the user supplies a password.
In a blog post Tuesday, Instagram said support for third-party authenticator apps “has begun to roll out and will be available to the global community in the coming weeks.
Instagram put me on a whitelist of accounts to get an early peek at the new security feature, so these options probably aren’t yet available to most users. But there’s a screenshot below that shows the multi-factor options available in the mobile app. When these options do become more widely available, Instagram says people can use a third-party app to receive a one-time code. To do this:
- Go to your Settings.
- Scroll down and tap Two-Factor Authentication.
- If you haven’t already turned two-factor authentication on, tap Get Started.
- Tap next to Authentication App, then follow the on-screen instructions.
- Enter the confirmation code from the third party authentication app to complete the process.
Note that if you have previously enabled SMS-based authentication, it is likely still enabled unless and until you disable it. The app also prompts users to save a series of recovery codes, which should be kept in a safe place in case one’s mobile device is ever lost.
WHAT IT DOESN’T FIX
Instagram has received quite a lot of bad press lately from publications reporting numerous people who had their accounts hijacked even though they had Instagram’s SMS authentication turned on. The thing is, many of those stories have been about people having their Instagram accounts hijacked because fraudsters were able to hijack their mobile phone number.
In these cases, the fraudsters were able to hijack the Instagram accounts because Instagram allows users to reset their account passwords with a single factor — using nothing more than a text message sent to a mobile number on file. And nothing in these new authentication offerings will change that for people who have shared their mobile number with Instagram.
Criminals can and do exploit SMS-based password reset requests to hijack Instagram accounts by executing unauthorized “SIM swaps,” i.e., tricking the target’s mobile provider into transferring the phone number to a device or account they control and intercepting the password reset link sent via SMS. Once they hijack the target’s mobile number, they can then reset the password for the associated Instagram account.
I asked Instagram if there was any way for people who have supplied the company with their phone number to turn off SMS-based password reset requests. I received this response from their PR folks:
“I can confirm that disabling SMS two factor will not disable the ability to reset a password via SMS,” a spokesperson said via email. “We recommend that the community use a third-party app for authentication, in place of SMS authentication. We’ll continue to iterate and improve on this product to keep people safe on our platform.”
Fraudulent SIM swaps illustrate the value of moving away from SMS-based authentication when more secure options are available. Doing so makes one less likely to be targeted by these phone number hijacks, which are generally perpetrated by determined, well-organized attackers.
The hard truth is that if an attacker wants control over your mobile number badly enough, he will get it. And if he does, he will likely gain access to far more than your Instagram account: Someone who hacks your phone number can then compromise any account that allows authentication or password resets via text message or automated phone call.
In May, KrebsOnSecurity documented the case of a Boston man who had his Instagram account hijacked after a crooked T-Mobile employee transferred his phone number to another device without authorization. Additionally, authorities in California and Florida have recently arrested several men accused of conducting similar attacks, and according to charging documents all of these individuals routinely worked with associates at mobile phone stores to carry out their heists.
In case you missed it, KrebsOnSecurity ran a story earlier this month about the sound security advice allegedly offered by one of the most accomplished SIM swappers of late, who recommended using Internet-based phone services like Google Voice in lieu of relying on mobile phone providers for multi-factor authentication.
Standard disclaimer: If SMS-based authentication is the strongest form of extra security a Web site offers, this is still far better than relying on just passwords for login security. If app-based options are available, take advantage of that. If the site in question offers hardware-based security keys, even better. Twofactorauth.org lists multi-factor authentication options for hundreds of sites, including probably many that you use on a daily basis. Take a moment this week to strengthen your login options.
Tags: Authy, Duo, Facebook, Google Authenticator, Google Voice, Instagram, SIM swap, T-Mobile, two-factor authentication, twofactorauth.org
You can skip to the end and leave a comment. Pinging is currently not allowed.

